Encryption, key to democracy
I’ve only ready a few stories on the Apple controversy, but I’m increasingly anxious, hoping civil liberties prevail. This is a bit of a journal entry combined with some comments I want to remember, so I’ll give a bit of background in case I read this in the future.
Background
The government wants Apple to make it possible to disable a phone’s automatic erase feature and allow for brute force password testing. This would ostensibly be for a specific phone for a specific case, but it’s easy to imagine the hack’s scope broadening, with or without public knowledge.
The Federal Bureau of Investigation (FBI) and Apple engaged in a dispute over whether the federal court may compel Apple to create and electronically sign new software that would enable the FBI to unlock an iPhone 5C it recovered from one of the shooters in a terrorist attack in San Bernardino, California, in December 2015. The attack killed 14 people and seriously injured 22. The two attackers later died in a shootout with police, having previously destroyed their personal phones; however, a work phone issued to one of the attackers by his employer was recovered intact. The phone is locked with a four-digit password. (Wikipedia)
It was also revealed Apple had already instructed the FBI on an existing way to get the data, but the FBI bungled the procedure. It seems it was just incompetence or negligence, but I have to wonder if the government was itching for an opportunity to compel Apple to give them a master key. An ACLU post claims it is already possible for the FBI to do what they want without Apple’s involvement, and provides instructions. This seems to indicate the government is interested in access to more than just this one phone.
Apple initially opposed the court order on grounds complying would pose a security risk for their customers. They are obviously correct, even though the government then argued it was simply a marketing based position.
Apple also asserts that being compelled to write new software “amounts to compelled speech and viewpoint discrimination in violation of the First Amendment. … [W]hat is to stop the government from demanding that Apple write code to turn on the microphone in aid of government surveillance, activate the video camera, surreptitiously record conversations, or turn on location services to track the phone’s user?”
Encryption is key
Encryption technology is now vital for a free society, and has been instrumental in exposing corruption in many countries, especially developing ones.
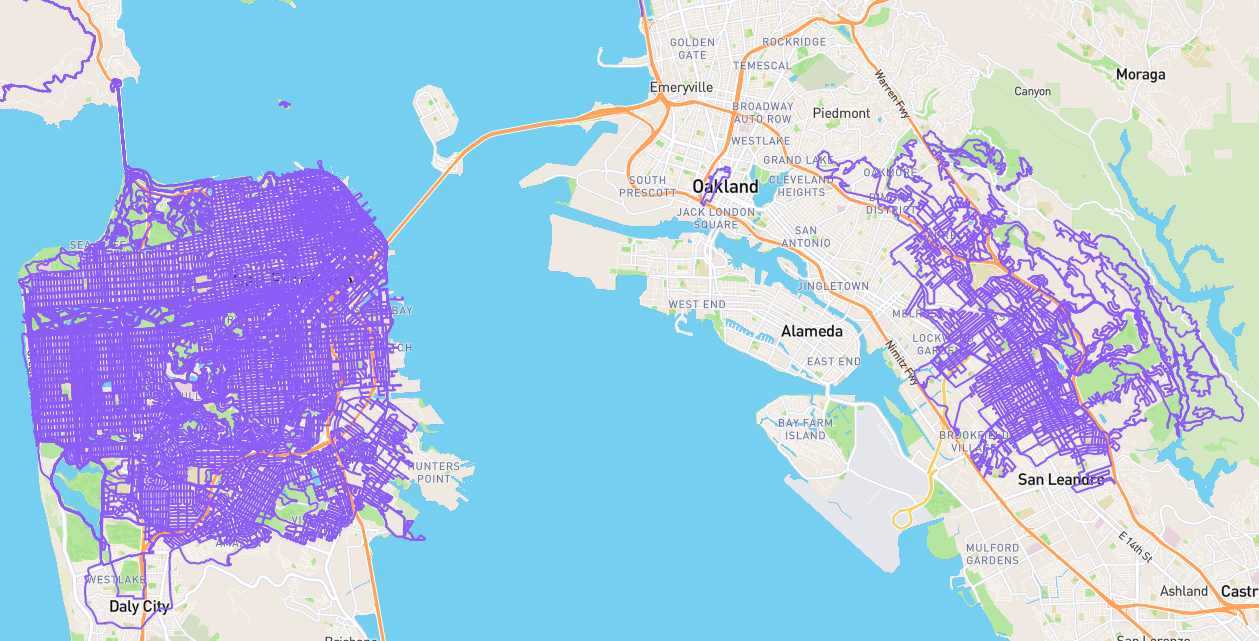
- There’s an ongoing battle where Medium’s HTTPS encryption is making it difficult for Malaysia to track readers and investigative journalists.
-
The Committee to Protect Journalists maintains a Journalist Security Guide that includes encryption tools and information.
In China, foreign correspondents have seen their personal computers infected with surveillance software that was concealed as attachments to carefully fabricated emails. Authorities in countries from Ethiopia to Colombia have accessed reporters’ telephone, email, and text conversations. Government players are not the only ones who use digital surveillance and sabotage; large criminal organizations increasingly exploit high-tech opportunities. Opportunistic or “patriotic” computer criminals also target journalists working with valuable or controversial data.
-
A year ago the International Center for Journalists reported on corruption in Latin America unearthed through their program that includes encryption training:
Journalists working in the IRIA program received security protocol training, including cybersecurity skills and training on tools such as Secure Reporter, an encrypted collaborative platform ICFJ built to help journalists work on joint investigations in a safe digital environment.
These are just a few examples. Sickening is the idea of any government, especially ones headed by brutal dictators, having access to not just online communications but every personal photo and detail someone might store on their devices. It’s bad enough the U.S. Department of Justice fought to force journalists to reveal their sources.
From TechDirt:
It is difficult to overstate the chilling impact this particular ruling will have on investigative journalism, especially when it comes to reporting on government abuse and corruption. Even if a journalist promises confidentiality and completely means it, this ruling means the government can just drag that journalist to court and force him or her to reveal his or her sources. That’s going to completely freak out whistleblowers. While the court disagrees, I have a hard time seeing how this does not, fundamentally, violate the First Amendment’s protections for press freedom.
Given that, I agree with Judge Gregory, who wrote a strong dissent.
Today we consider the importance of a free press in ensuring the informed public debate critical to citizens’ oversight of their democratically elected representatives. Undoubtedly, the revelation of some government secrets is too damaging to our country’s national security to warrant protection by evidentiary privilege. Yet the trial by press of secret government actions can expose misguided policies, poor planning, and worse. More importantly, a free and vigorous press is an indispensable part of a system of democratic government. Our country’s Founders established the First Amendment’s guarantee of a free press as a recognition that a government unaccountable to public discourse renders that essential element of democracy – the vote – meaningless. The majority reads narrowly the law governing the protection of a reporter from revealing his sources, a decision that is, in my view, contrary to the will and wisdom of our Founders.
If governments don’t even need to bother with courts and warrants, and can instead directly access journalist’s or anyone’s phones, we can hardly expect the government to exercise any restraint in doing so. As Edward Snowden has revealed, the government not only runs many surveillance programs we previously didn’t know were possible, but they have lied about existence of programs even after the programs were proven to exist.
If Apple must comply, must individual employees?
Today the New York Times explored a scenario where Apple might lose but be unable to comply due to individual employees refusing to do the work.
Apple employees are already discussing what they will do if ordered to help law enforcement authorities. Some say they may balk at the work, while others may even quit their high-paying jobs rather than undermine the security of the software they have already created, according to more than a half-dozen current and former Apple employees.
If a company is truly not compliant with the law, it seems that company would be responsible for complying or be penalized. Perhaps there is room for an exception based on a good faith effort to comply at the company level, despite not being able to find individual employees to carry out the work. But short of some exception, I have to wonder what would happen in the case where every employee at a company quit rather than doing the work, and no company remained.
The government has cracked down on tech companies in the past. A judge imposed a $10,000-a-day penalty on the email service Lavabit when it did not give its digital encryption keys to investigators pursuing information on Edward J. Snowden, the former intelligence contractor who leaked documents about government surveillance.
The small company’s response could be indicative of how individual Apple employees reacted to a court order. When Lavabit was held in contempt, its owner shut down the company rather than comply.
At least for individual employees, I think they are 100 percent within their rights to refuse to do work that violates their integrity, especially when they feel the work undermines the very democratic system we supposedly believe in. A number of comments on the NYT piece were interesting:
-
In response to BILL, who wrote “FINE, The Jails have plenty of room for criminals who refuse to accept a court order. Apple’s boys will fit in just fine.”, Barbarika of Wisconsin writes:
Dear Bill, Lets say you are a locksmith who makes an honest living. One fine day, a dictator (lets assume Trump) orders you to create a master key which can open all doors in your neighbourhood to catch a suspected thief. Considering your comment, you will jump in affirmation to such a request, and then how will this shining beacon of liberty be different than land of Borat (no offense to Kazakhstan) * nbafan of ohio:
It’s not about the one person, it’s about setting a precedent. If you can decrypt the phone of someone who committed an act of terrorism, what’s stopping you from decrypting the phone of someone suspected of committing terrorism? And if now we’re all fine with decrypting the phones of people suspected of doing something, what’s stopping us from decrypting the phones of people suspected of dealing drugs during a routine traffic stop?
-
The Buddy of Astoria, NY:
In an employment at will environment, the engineers would be within their rights to end their relationship with their employer Apple, and thus remove themselves from the legal controversy. It wouldn’t be the first time a worker left a company because he was asked to do something that made him feel dishonest.
-
William of Los Angeles:
If a Govt. worker can refuse to issue a marriage license because of religious beliefs, why can’t a company of people who make telephones refuse to mutilate their product so the Govt.can gain information and data of a personal nature from the citizens who use this phone…on principal.
-
Mardak of Boston:
I am not a fan of Apple and its management and I was even less so during the great industrialist Steve Jobs’ days. The Apple stance for privacy has certainly made me develop new found respect for them. I expected them to fold like tents if their share prices were threatened. I don’t expect any principled stance from a multinational corporation. However, this new development warms my heart as an engineer. It’s time software and hardware engineers started to realize that in the battle for privacy and civil rights in the face of ubiquitous technology, we are in the front lines! We ARE the front lines. Geeks eager to please management have to realize there is more to this than the next promotion or other pat on the back. If we don’t draw a virtual line in the sand, management certainly won’t.
The company whose most famous public statement is historical 1984 Ad campaign must realize it can’t be a party to bringing about the 1984-like state where privacy is merely a quaint notion from a distant past. -
Woof of NY:
A sense of proportionality is needed here.
First: The FBI has the content of the phone, except for the last 4 weeks, from the cloud back up. Judging on what the FBI has released to date, that backup contains no relevant information
Second: The phone is the work phone . The attackers had 2 private phones, that they used to plan the attack.
Third: The attackers took care to destroy those two private phones. They did not destroy the work phone. The strong implication is that it contains nothing relevant to the attack.
Fourth: The FBI chose a public fight, rather than using the secret FISA court indicating that it is interested not in the content of that single phone, but all phones in the US.
On balance, the available evidence is that the FBI has a weak cause in demanding an action that with high probability send sales in foreign countries of America’s most valuable company spiraling downwards.
Final note:
In an ironic twist, the government of Kazakhstan is outlawing the use of smart phones by its police and public employee because they leak too many embarrassing facts about the government via WhatsApp to the public.
If the FBI succeeds, those leaks, that are the only available check by the people on a dictatorial government , will soon fade into oblivion all over the world,